��ƪ�����ᵽ��Ring0�����Ring3���ַ��У�鷽��,�ҽ�Դ���е�ʵ�ַŵ�����:
�����ж��Ƿ�Խ����Ǹ���:
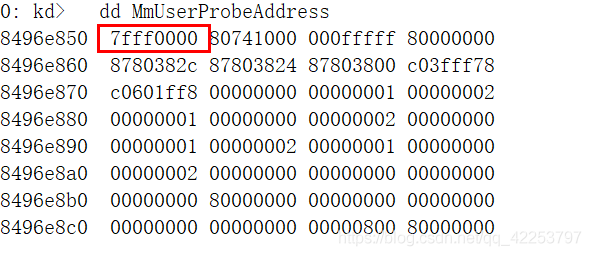
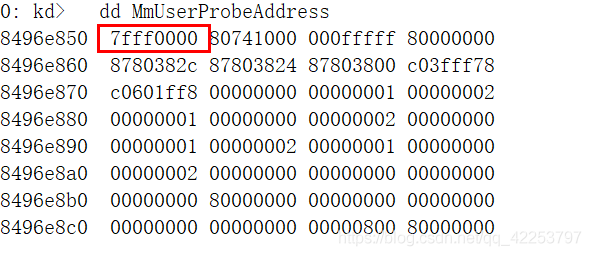
MmUserProbeAddress,��Դ����û���ҵ����Ķ���,������Windbg���˿���
Windbg:
VOID
NTAPI
ProbeForRead(IN CONST VOID *Address,
IN SIZE_T Length,
IN ULONG Alignment)
{
ULONG_PTR Last, Current = (ULONG_PTR)Address;
PAGED_CODE();
if (Length != 0)
{
ASSERT((Alignment == 1) ||
(Alignment == 2) ||
(Alignment == 4) ||
(Alignment == 8) ||
(Alignment == 16));
if ((Current & (Alignment - 1)) != 0)
{
ExRaiseDatatypeMisalignment();
}
Last = Current + Length - 1;
if ((Last < Current) || (Last >= (ULONG_PTR)MmUserProbeAddress))
{
ExRaiseAccessViolation();
}
}
}
������������ҳ���Ƿ����д
VOID
NTAPI
ProbeForWrite(IN PVOID Address,
IN SIZE_T Length,
IN ULONG Alignment)
{
ULONG_PTR Last, Current = (ULONG_PTR)Address;
PAGED_CODE();
if (Length != 0)
{
ASSERT((Alignment == 1) ||
(Alignment == 2) ||
(Alignment == 4) ||
(Alignment == 8) ||
(Alignment == 16));
if ((Current & (Alignment - 1)) != 0)
{
ExRaiseDatatypeMisalignment();
}
Last = Current + Length - 1;
if ((Last < Current) || (Last >= (ULONG_PTR)MmUserProbeAddress))
{
ExRaiseAccessViolation();
}
Last = PAGE_ROUND_DOWN(Last) + PAGE_SIZE;
do
{
*(volatile CHAR*)Current = *(volatile CHAR*)Current;
Current = PAGE_ROUND_DOWN(Current) + PAGE_SIZE;
} while (Current != Last);
}
}
����������η����,�ɷ�δ�������١����C���
�����:
ReactosԴ��
cs